Did you know that there was over $500 million dollars of consumer loss for data breaches in 2023? (According to the 2023 IC3 annual report.)
One way cybercriminals can gain access to accounts during a data breach is by using credential stuffing attacks. Credential stuffing or stealing attacks use stolen usernames and passwords to attempt to take over a user’s account. This process is repeated over and over while cybercriminals try to find a successful match in order to takeover an account.
Angel Belford
Recent Posts
What is a credential stuffing attack?
May 8, 2024 12:57:08 PM / by Angel Belford posted in Security, data breach
Protect Your Business from Deepfake and Generative AI Threats
Mar 18, 2024 11:15:56 AM / by Angel Belford posted in Security, deepfake, ai
You are probably aware of the growing trend of deepfakes, and the cybersecurity challenges created by this technology.
Read on and find out more about this evolving security threat and how to protect yourself.
What to do if I clicked on a phishing email?
Feb 7, 2024 1:31:31 PM / by Angel Belford posted in phishing, cybersecurity
One of the most common types of cybersecurity attacks is phishing. Phishing is when criminals use fake emails to lure you into clicking on them and handing over your personal information or installing malware on your device that can lead to a security compromise.
If you have clicked on a phishing email, complete the steps below to reduce the damage.
If this occurs when you are working in an office, notify the IT department immediately.
Holiday Shopping Safety Tips
Dec 1, 2023 9:48:47 AM / by Angel Belford posted in phishing, cybersecurity, travel, holiday
Now that holiday shopping is in full swing, below are a few online shopping trends with tips about how to stay safe online while buying gifts for everyone on your list.
Generally, experts seem to believe that the average American is going to spend less this year – though pandemic restrictions have largely lifted, we've entered a new season of economic uncertainty. This means every dollar is even more important, which is why we want to help you protect your hard-earned cash from the scammers and hackers that popup every year. It's like they don't care about the naughty list!
Here is what we think is cheerful and what we think is coal-worthy for shopping online this holiday season:
phishing cybersecurity travel holiday
When Cybercriminals Go Phishing Don’t Take the Bait
Sep 25, 2023 4:30:50 PM / by Angel Belford posted in phishing, cybersecurity
Phishing is when criminals use fake emails, social media posts, or direct messages with the goal of luring you to click on a bad link or download a malicious attachment. If you click on a phishing link or file, you can hand over your personal information to the cybercriminals. A phishing scheme can also install malware onto your device.
Easily Boost your Cybersecurity by Keeping Software and Apps Updated
Sep 25, 2023 10:51:00 AM / by Angel Belford posted in passwords, cybersecurity, software updates
If you install the latest updates for devices, software, and apps, not only are you getting the best security available, but you also ensure that you get access to the latest features and upgrades. However, you can only benefit if you update! Don’t fret, updating software is easy, and you can even make it automatic.
passwords cybersecurity software updates
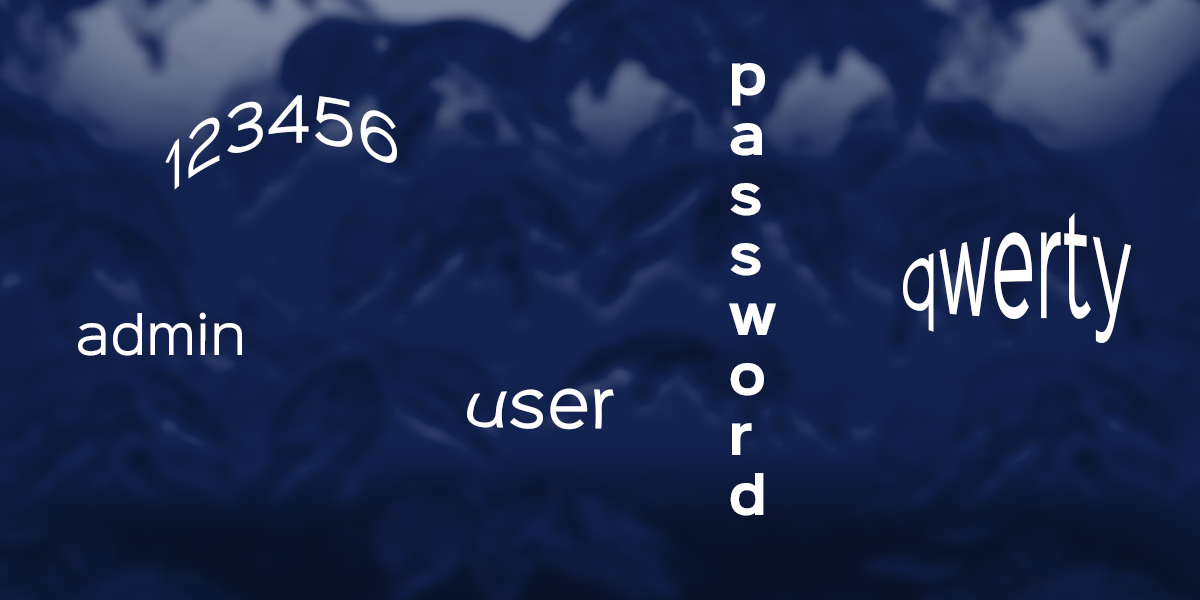
Ditch the Notebook and Keep your Passwords Safe
Sep 25, 2023 10:18:35 AM / by Angel Belford posted in passwords, cybersecurity, password manager
Passwords are your first line of defense against cybercriminals and data breaches and can be made ironclad with MFA (multi-factor authentication).
passwords cybersecurity password manager
Protect Yourself in Multiple Ways with Multi-Factor Authentication
Sep 22, 2023 4:38:30 PM / by Angel Belford posted in Multi-Factor Authentication, cybersecurity
Wouldn’t it be nice if you could protect your password with another password? Multi-factor authentication gives you this power – think of it like placing your housekeys in a safety deposit box that can only be opened by a facial scan. In some cases, this metaphor isn’t far off from reality.
Multi-Factor Authentication cybersecurity
Still Just Using Anti-Malware for Threat Monitoring?
Aug 30, 2023 1:39:03 PM / by Angel Belford posted in cybersecurity, threat monitoring
As part of our security services, our proactive threat hunting solutions include Endpoint Detection and Response (EDR) and Security Information and Event Management (SIEM) monitoring.
cybersecurity threat monitoring
Are you Prepared for a Ransomware Attack?
Jul 25, 2023 9:11:12 AM / by Angel Belford posted in Security, ransomware
Did you know that 85% of organizations have experienced at least one ransomware attack in the last year?